Programming languages play an important role in our modern-day lives. Without these languages, building software, games and webpages would be much different than it is today. While many sites and companies use different languages, one of the most popular is the PHP language.
PHP is used by nearly 80% of all websites where the language is known and is best for making interactive web pages, but can also do so much more. PHP 7 was first released in 2015 and had many different features that programmers and developers loved. However, the release of PHP 7 wasn’t without its issues.
In particular, there were 3 zero day flaws that hit PHP 7 quite hard and provided a lot of trouble for many users. This article is going to look at what these flaws were, what they did, what could have happened if they weren’t patched and some general security tips for those using PHP.
Defining a Zero-Day Vulnerability
Before we look at the harmful zero day vulnerabilities that affected PHP 7, we need to look at zero day vulnerabilities in general. A zero-day vulnerability is a software flaw that is unknown to those usually in charge of fixing it. The reason it is called a zero-day vulnerability is because of the fact it was just newly discovered.
This means that the team has had “zero-days” to fix it or patch it. As a result, those who are using your software or program could be at risk as there is no protection in place yet. Because of this increased risk, teams need to work quickly to patch these flaws, before people exploit and take advantage of it. If not, your entire software or program could be in jeopardy. That’s why is good to have PHP logging software to help you analyze the situation.
The 3 Zero-Day Vulnerabilities Found in PHP 7
In total, PHP 7 had three zero day vulnerabilities that existed. While they were all patched and dealt with, if they hadn’t have been, it could have been awful for users. These flaws were:
– CVE-2016-7478—Remote Denial of Service
– CVE-2016-7479—Use-After-Free Code Execution
– CVE-2016-7480—Use of Uninitialized Value Code Execution
Something that all of these vulnerabilities have in common is that they related to the unserialize function within PHP 7. Thankfully, it was reported that no hackers were able to exploit these flaws while they were active. They were quickly patched, but their existence is still a cautionary tale to all software teams out there to be careful.
The Flaws Were Patched, But What if They Weren’t?
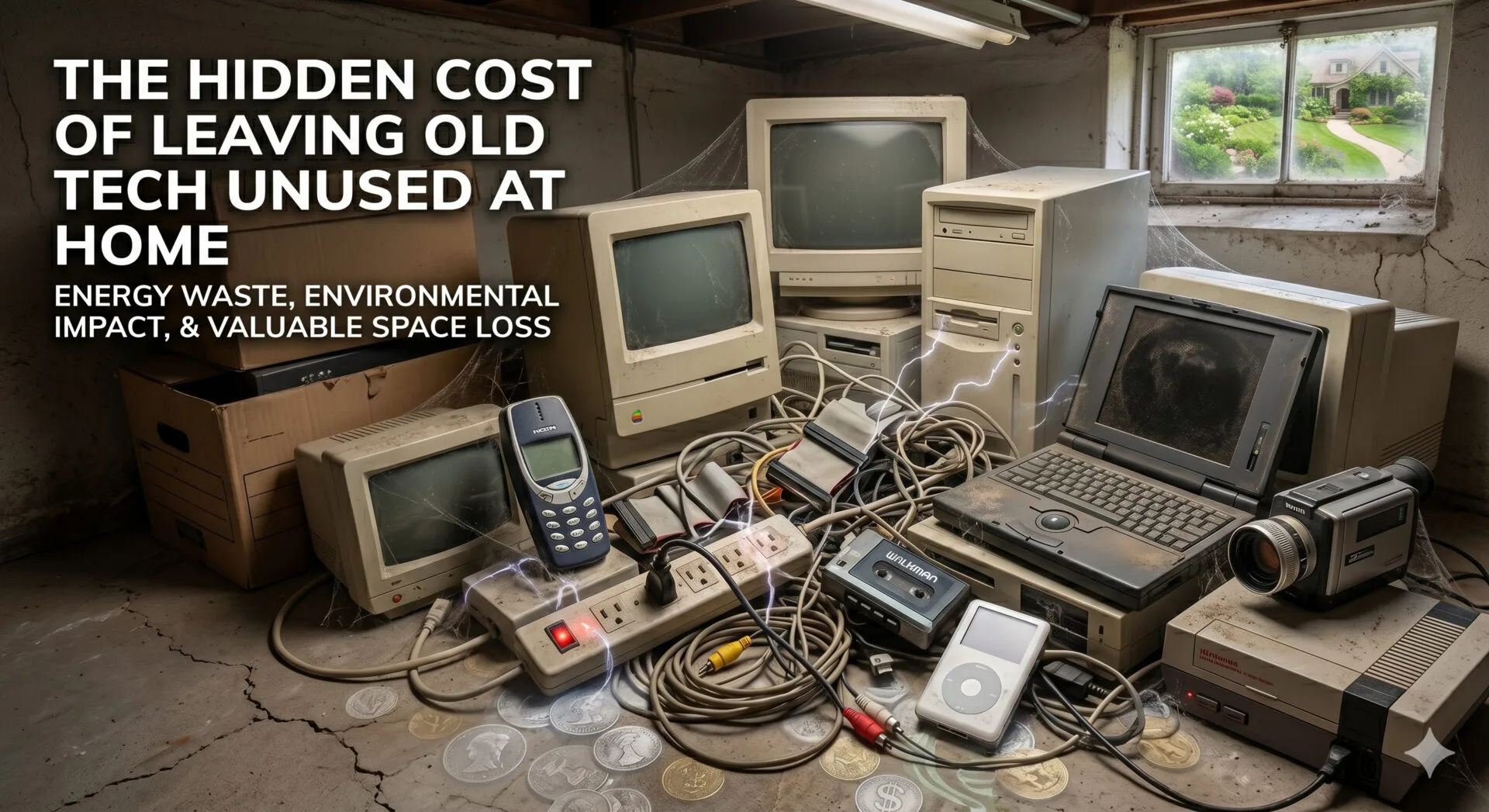
As mentioned, these flaws were all fixed up and patched quickly, but what would have happened if they weren’t? Well, it could have negatively affected thousands of web pages in a big way. Hackers could have taken over your server, created a DDoS attack and so much more. In addition to the direct damage, many sites would have gone through, there would’ve been some indirect damage.
A lot of sites would have likely lost a lot of users and revenue due to their site being down or compromised. If a full-on hack or data breach occurred, and personal information was stolen, your site could have been sued for a lot of money, as well.
Security Tips When Using PHP
While the aforementioned zero day vulnerabilities are no longer a problem for PHP 7 users, it is still important to always keep security in mind. Keeping security as a major priority will ensure any future issues or exploits don’t affect you as much as they could. One of the most important things you can do is to upgrade and update your software frequently.
Patches and fixes for flaws or vulnerabilities are often released in updated versions, so skipping these updates can leave you vulnerable. Using tools to analyze your code is also a good practice to take up, to make sure you are always kept in the know.
You might also like to read Why Is Laravel An Ideal PHP Framework For Development?
Some of these tools can even let you know when issues or vulnerabilities might be present. Of course, practicing safe coding practices and checking to make sure everything is accurate is also recommended. Everyone working on your code should have a good understanding of it and be aware of how to do their job effectively and safely.
In conclusion, hopefully, this article has taught you about the zero-day flaws that were present in PHP 7, and why security is so important.


Leave a Reply